WHite paper
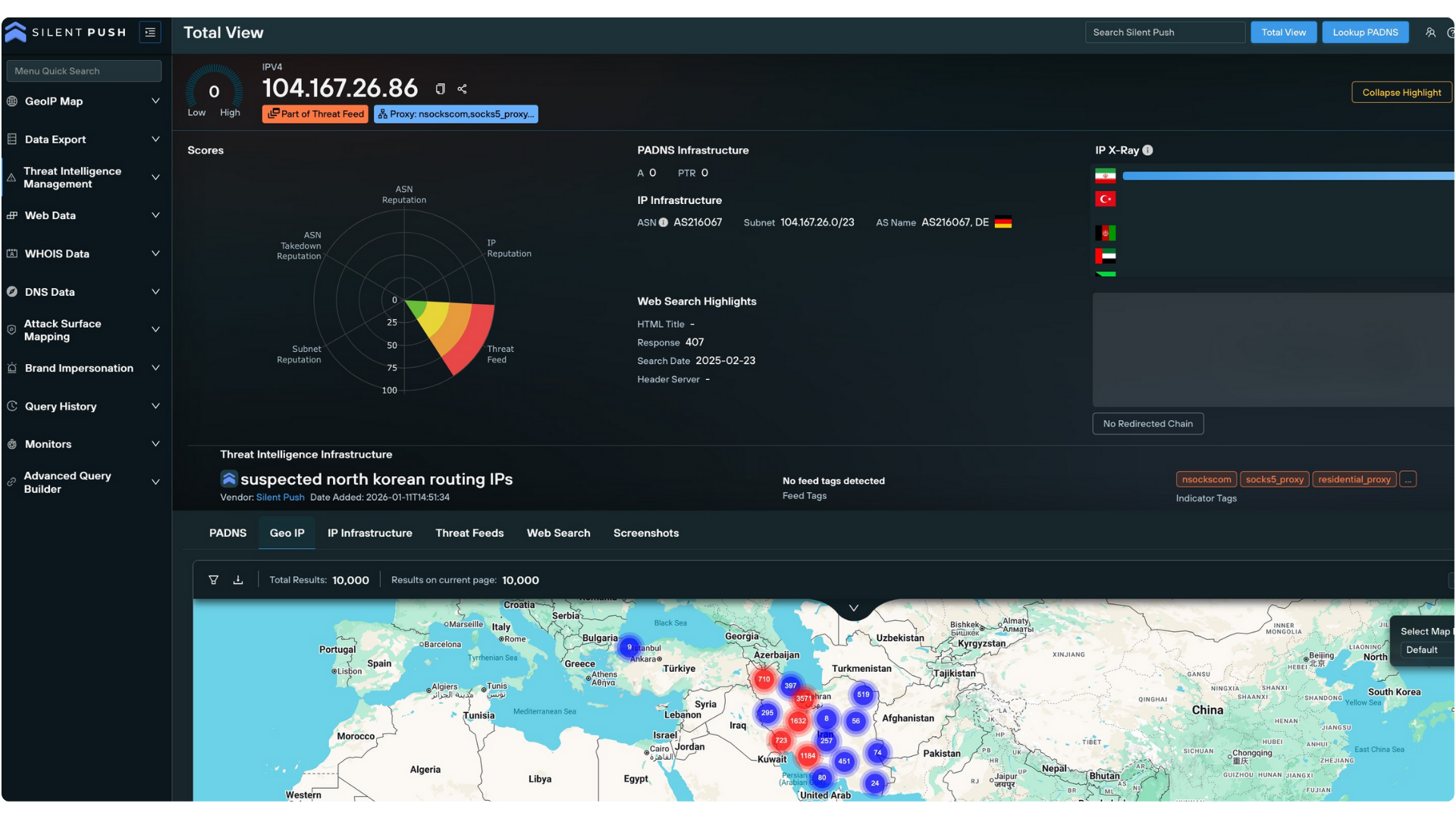
Adversaries hide in plain sight by mimicking employee footprints. When attackers mask their true location via residential proxies, traditional perimeters fail to see the threat.
what to expect
Unmask the True Origin: Move beyond deceptive geolocations to identify the true country of origin for every connection.
Optimize Security Ops: Reduce alert fatigue and investigation times by replacing ambiguous IP data with definitive, verifiable origin intelligence.
Automate Proactive Defense: Integrate high-confidence origin data into your SIEM and IdP to block location deception in real-time.
Your platform gives a super-unique perspective into threat intelligence, this is clearly the future. – Professional Services Big Four Company
This is impressive, the dexterity around what you can find. We’ve never seen anything else. It’s exciting. – Intelligence Team for ISAC
You have the most complete view of DNS activity compared to any service we have used. – Fortune 500 Financial Services Company
About silent push
Silent Push enables preemptive cyber defense by exposing threat actor infrastructure as it’s being set up, using Indicators of Future Attack (IOFA)™.
By mapping the internet from an attacker's perspective, Silent Push enables security teams to neutralize threats before an attack is launched, moving beyond the limitations of reactive cybersecurity.
TRAFFIC ORIGIN
Go beyond the IP to reveal the real country of origin for a connection, unmasking the proxy layers used by fraudulent hires and state-sponsored actors.